108389
Sep 20, 2012, updated at 13:51:31 (UTC)
Meine Cisco Access Points, der Radius Server, das LDAP und ich.
Hallo Admins,
mir geht es ähnlich wie folgendem Kollegen: ( Fehlende Konfigurationsinformationen zu RADIUS-Servern )
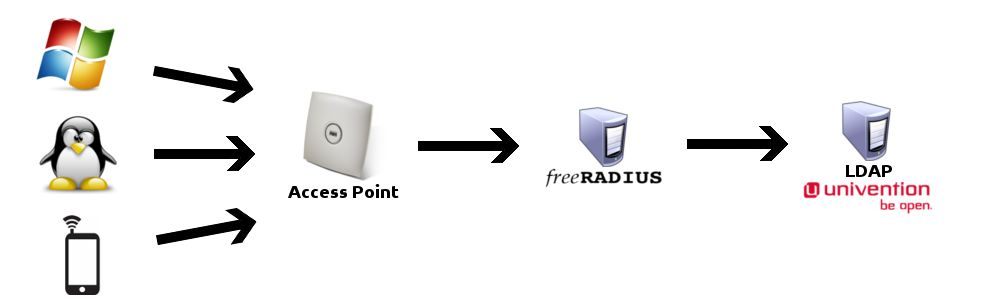
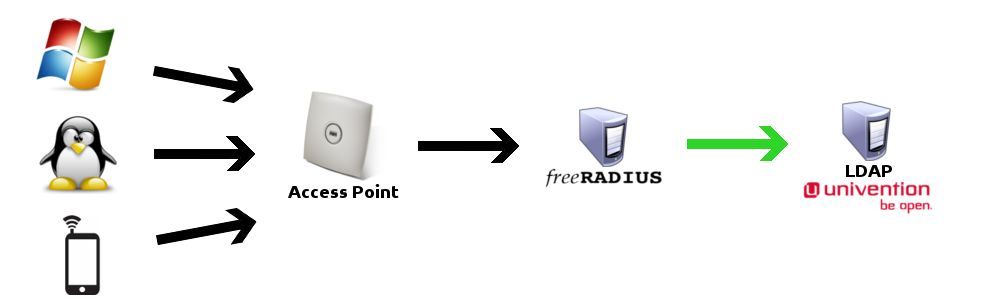
Aktuell stellen wir den ca. 200 Mitarbeitern ein WLAN zur Verfügung, welches mittels Cisco Aironet 1130 WLAN Routern überall im Haus verfügbar ist. Verschlüsselt ist das WLAN mit WPA2-PSK, es gibt also ein allgemeines Passwort, ein so genanntes “Shared Secret”, das heißt, dass theoretisch jeder der 200 Mitarbeiter das Passwort kennen darf. Benötigt nun ein Mitarbeiter Zugriff auf das WLAN muss er bei der Administration das Passwort erfragen.
Da es sich bei dem Passwort um ein “Shared Secret” handelt, muss das Passwort bei jedem Austritt eines Mitarbeiters geändert werden, um unautorisierte Zugriffe zu vermeiden. Da es ab einer gewissen Größe eines Unternehmens unsicher ist den Zugriff über ein “Shared Secret” zu gewähren, zumal es eine hohe Mitarbeiterfluktuation gibt, verursacht die aktuelle Methode einen sehr hohen Arbeitsaufwand.
Um zukünftig das WLAN besser abzusichern und den hohen Arbeitsaufwand durch die ständige Änderung des WLAN Passwortes zu vermeiden, habe ich den Auftrag bekommen, eine Alternative mit LDAP Anbindung zu finden und umzusetzen.
Der LDAP Server ist mir Vorgegeben, als Radiusserver habe ich ein Debian Squeeze (6.0.5) installiert und FreeRADIUS Version 2.1.10 über die Paketquellen installiert. Wie oben erwähnt habe ich Cisco Aironet 1130 WLAN Router bzw. Access Points zur Verfügung. Ich selber nutze ein Ubuntu 12.04.
Verschiedensten Anleitungen aus den Tiefen des Internets habe ich entnommen das man dem Radiusserver den LDAP Server bekannt machen sollte.
-- Hier also meine radiusd.conf vom Radius-Server.
Im Bereich "MODULE CONFIGURATION" steht, dass viele Modul configs nach /etc/freeradius/modules/ ausgelagert wurden.
Da ich einen Ldap-Server eintragen möchte schaue ich mir die /etc/freeradius/modules/ldap an.
-- Hier meine /etc/freeradius/modules/ldap vom Radius-Server.
Die /etc/freeradius/modules/ldap war vorher leer, es stand nur "ldap{}" drin.
Dann habe ich meinen Ldap Server dort eingetragen und jetzt sieht die /etc/freeradius/modules/ldap so aus wie oben zu sehen.
Weil ich dann mal testen wollte ob der Radius-Server auch mit dem Ldap Server spricht habe ich den Befehl "radtest" rausgekramt.
-- Der Befehl radtest
-- Erster Versuch mit radtest
testuser und passwort123 sind verfremdet, aber garantiert im Ldap vorhanden. Richtig sind die Zugangsdaten auch.
172.26.100.1 ist die IP-Adresse vom Radius-Server.
Die NAS-Port-Number kann man sich laut http://linux.die.net/man/1/radtest aussuchen.
Das Secret ist das was ich vorher in der /etc/freeradius/clients.conf festgelegt habe.
-- Zweiter Versuch mit radtest
Ähnlich wie der erste Versuch, diesmal allerdings mit der localhost Adresse.
Beim Radius-Server bekomme ich dann folgende Reaktion raus.
-- Radius-Server Reaktion auf meinen zweiten Login Versuch
Daraus habe ich entnommen, dass der testuser nicht in der LDAP-Gruppe WLAN ist. Als ich den testuser aber hinzugefügt habe und die Anfrage immer noch nicht geklappt hat, habe ich mir die Debug-Ausgabe gründlicher durchgelesen und festgestellt, dass der Standard "groupmembership-filter" verwendet wird, welcher in der /etc/freeradius/sites-enabled/inner-tunnel definiert ist.
Also habe ich mir einen neuen "groupmembership-filter" gebastelt.
Welcher überraschenderweise funktioniert.
-- Nächster Versuch mit radtest
Nun stehe ich vor der Herausforderung meinen Cisco Access Point dazu zu bringen mit meinem Radius-Server zu sprechen.
Bitten und betteln sowie dem AP gut zureden hat bis jetzt nicht funktioniert. Genau so wenig wie einige der vielen Tutorials welche ich in den untiefen des Internets (unter anderem auch hier auf administrator.de) gefunden habe.
Hat jemand einen Tipp für mich oder vielleicht auch eine Anleitung wie ich meinen Cisco Aironet 1130ag konfigurieren muss damit er mit meinem Radius spricht?
Auf der Weboberfläche des AP habe ich den Radius-Server eingetragen, allerdings sieht es so aus, dass die Anfrage nie beim Radius ankommt. Kann ich dem AP irgendwie die Logfiles entlocken? Vielleicht über das Terminal per ssh Verbindung?
-- Ein telnet von meinem AP auf den Radius-Server funktioniert nicht.
-- netstat -tulpen sagt mir, dass der Radius-Server aber eigentlich zuhören sollte.
Bin mittlerweile zu dem Schluss gekommen, dass telnet kein udp kann.
Bei einem telnet auf einen port der tcp kann kam der Kommentar "Open" zurück.
Vielen Dank und viele Grüße
farenz
mir geht es ähnlich wie folgendem Kollegen: ( Fehlende Konfigurationsinformationen zu RADIUS-Servern )
Aktuell stellen wir den ca. 200 Mitarbeitern ein WLAN zur Verfügung, welches mittels Cisco Aironet 1130 WLAN Routern überall im Haus verfügbar ist. Verschlüsselt ist das WLAN mit WPA2-PSK, es gibt also ein allgemeines Passwort, ein so genanntes “Shared Secret”, das heißt, dass theoretisch jeder der 200 Mitarbeiter das Passwort kennen darf. Benötigt nun ein Mitarbeiter Zugriff auf das WLAN muss er bei der Administration das Passwort erfragen.
Da es sich bei dem Passwort um ein “Shared Secret” handelt, muss das Passwort bei jedem Austritt eines Mitarbeiters geändert werden, um unautorisierte Zugriffe zu vermeiden. Da es ab einer gewissen Größe eines Unternehmens unsicher ist den Zugriff über ein “Shared Secret” zu gewähren, zumal es eine hohe Mitarbeiterfluktuation gibt, verursacht die aktuelle Methode einen sehr hohen Arbeitsaufwand.
Um zukünftig das WLAN besser abzusichern und den hohen Arbeitsaufwand durch die ständige Änderung des WLAN Passwortes zu vermeiden, habe ich den Auftrag bekommen, eine Alternative mit LDAP Anbindung zu finden und umzusetzen.
Der LDAP Server ist mir Vorgegeben, als Radiusserver habe ich ein Debian Squeeze (6.0.5) installiert und FreeRADIUS Version 2.1.10 über die Paketquellen installiert. Wie oben erwähnt habe ich Cisco Aironet 1130 WLAN Router bzw. Access Points zur Verfügung. Ich selber nutze ein Ubuntu 12.04.
Verschiedensten Anleitungen aus den Tiefen des Internets habe ich entnommen das man dem Radiusserver den LDAP Server bekannt machen sollte.
-- Hier also meine radiusd.conf vom Radius-Server.
#####################################################################
## radiusd.conf -- FreeRADIUS server configuration file.
##
## http://www.freeradius.org/
## $Id$
##
######################################################################
#
# Read "man radiusd" before editing this file. See the section
# titled DEBUGGING. It outlines a method where you can quickly
# obtain the configuration you want, without running into
# trouble.
#
# Run the server in debugging mode, and READ the output.
#
# $ radiusd -X
#
# We cannot emphasize this point strongly enough. The vast
# majority of problems can be solved by carefully reading the
# debugging output, which includes warnings about common issues,
# and suggestions for how they may be fixed.
#
# There may be a lot of output, but look carefully for words like:
# "warning", "error", "reject", or "failure". The messages there
# will usually be enough to guide you to a solution.
#
# If you are going to ask a question on the mailing list, th
# explain what you are trying to do, and include the output from
# debugging mode (radiusd -X). Failure to do so means that all
# of the responses to your question will be people telling you
# to "post the output of radiusd -X".
######################################################################
#
# The location of other config files and logfiles are declared
# in this file.
#
# Also general configuration for modules can be done in this
# file, it is exported through the API to modules that ask for
# it.
#
# See "man radiusd.conf" for documentation on the format of this
# file. Note that the individual configuration items are NOT
# documented in that "man" page. They are only documented here,
# in the comments.
#
# As of 2.0.0, FreeRADIUS supports a simple processing language
# in the "authorize", "authenticate", "accounting", etc. sections.
# See "man unlang" for details.
#
prefix = /usr
exec_prefix = /usr
sysconfdir = /etc
localstatedir = /var
sbindir = ${exec_prefix}/sbin
logdir = /var/log/freeradius
raddbdir = /etc/freeradius
radacctdir = ${logdir}/radacct
#
# name of the running server. See also the "-n" command-line option.
name = freeradius
# Location of config and logfiles.
confdir = ${raddbdir}
run_dir = ${localstatedir}/run/${name}
# Should likely be ${localstatedir}/lib/radiusd
db_dir = ${raddbdir}
#
# libdir: Where to find the rlm_* modules.
#
# This should be automatically set at configuration time.
#
# If the server builds and installs, but fails at execution time
# with an 'undefined symbol' error, then you can use the libdir
# directive to work around the problem.
#
# The cause is usually that a library has been installed on your
# system in a place where the dynamic linker CANNOT find it. When
# executing as root (or another user), your personal environment MAY
# be set up to allow the dynamic linker to find the library. When
# executing as a daemon, FreeRADIUS MAY NOT have the same
# personalized configuration.
#
# To work around the problem, find out which library contains that symbol,
# and add the directory containing that library to the end of 'libdir',
# with a colon separating the directory names. NO spaces are allowed.
#
# e.g. libdir = /usr/local/lib:/opt/package/lib
#
# You can also try setting the LD_LIBRARY_PATH environment variable
# in a script which starts the server.
#
# If that does not work, then you can re-configure and re-build the
# server to NOT use shared libraries, via:
#
# ./configure --disable-shared
# make
# make install
#
libdir = /usr/lib/freeradius
# pidfile: Where to place the PID of the RADIUS server.
#
# The server may be signalled while it's running by using this
# file.
#
# This file is written when ONLY running in daemon mode.
#
# e.g.: kill -HUP `cat /var/run/radiusd/radiusd.pid`
#
pidfile = ${run_dir}/${name}.pid
# chroot: directory where the server does "chroot".
#
# The chroot is done very early in the process of starting the server.
# After the chroot has been performed it switches to the "user" listed
# below (which MUST be specified). If "group" is specified, it switchs
# to that group, too. Any other groups listed for the specified "user"
# in "/etc/group" are also added as part of this process.
#
# The current working directory (chdir / cd) is left *outside* of the
# chroot until all of the modules have been initialized. This allows
# the "raddb" directory to be left outside of the chroot. Once the
# modules have been initialized, it does a "chdir" to ${logdir}. This
# means that it should be impossible to break out of the chroot.
#
# If you are worried about security issues related to this use of chdir,
# then simply ensure that the "raddb" directory is inside of the chroot,
# end be sure to do "cd raddb" BEFORE starting the server.
#
# If the server is statically linked, then the only files that have
# to exist in the chroot are ${run_dir} and ${logdir}. If you do the
# "cd raddb" as discussed above, then the "raddb" directory has to be
# inside of the chroot directory, too.
#
#chroot = /path/to/chroot/directory
# user/group: The name (or #number) of the user/group to run radiusd as.
#
# If these are commented out, the server will run as the user/group
# that started it. In order to change to a different user/group, you
# MUST be root ( or have root privleges ) to start the server.
#
# We STRONGLY recommend that you run the server with as few permissions
# as possible. That is, if you're not using shadow passwords, the
# user and group items below should be set to radius'.
#
# NOTE that some kernels refuse to setgid(group) when the value of
# (unsigned)group is above 60000; don't use group nobody on these systems!
#
# On systems with shadow passwords, you might have to set 'group = shadow'
# for the server to be able to read the shadow password file. If you can
# authenticate users while in debug mode, but not in daemon mode, it may be
# that the debugging mode server is running as a user that can read the
# shadow info, and the user listed below can not.
#
# The server will also try to use "initgroups" to read /etc/groups.
# It will join all groups where "user" is a member. This can allow
# for some finer-grained access controls.
#
user = freerad
group = freerad
# max_request_time: The maximum time (in seconds) to handle a request.
#
# Requests which take more time than this to process may be killed, and
# a REJECT message is returned.
#
# WARNING: If you notice that requests take a long time to be handled,
# then this MAY INDICATE a bug in the server, in one of the modules
# used to handle a request, OR in your local configuration.
#
# This problem is most often seen when using an SQL database. If it takes
# more than a second or two to receive an answer from the SQL database,
# then it probably means that you haven't indexed the database. See your
# SQL server documentation for more information.
#
# Useful range of values: 5 to 120
#
max_request_time = 30
# cleanup_delay: The time to wait (in seconds) before cleaning up
# a reply which was sent to the NAS.
#
# The RADIUS request is normally cached internally for a short period
# of time, after the reply is sent to the NAS. The reply packet may be
# lost in the network, and the NAS will not see it. The NAS will then
# re-send the request, and the server will respond quickly with the
# cached reply.
#
# If this value is set too low, then duplicate requests from the NAS
# MAY NOT be detected, and will instead be handled as seperate requests.
#
# If this value is set too high, then the server will cache too many
# requests, and some new requests may get blocked. (See 'max_requests'.)
#
# Useful range of values: 2 to 10
#
cleanup_delay = 5
# max_requests: The maximum number of requests which the server keeps
# track of. This should be 256 multiplied by the number of clients.
# e.g. With 4 clients, this number should be 1024.
#
# If this number is too low, then when the server becomes busy,
# it will not respond to any new requests, until the 'cleanup_delay'
# time has passed, and it has removed the old requests.
#
# If this number is set too high, then the server will use a bit more
# memory for no real benefit.
#
# If you aren't sure what it should be set to, it's better to set it
# too high than too low. Setting it to 1000 per client is probably
# the highest it should be.
#
# Useful range of values: 256 to infinity
#
max_requests = 1024
# listen: Make the server listen on a particular IP address, and send
# replies out from that address. This directive is most useful for
# hosts with multiple IP addresses on one interface.
#
# If you want the server to listen on additional addresses, or on
# additionnal ports, you can use multiple "listen" sections.
#
# Each section make the server listen for only one type of packet,
# therefore authentication and accounting have to be configured in
# different sections.
#
# The server ignore all "listen" section if you are using '-i' and '-p'
# on the command line.
#
listen {
# Type of packets to listen for.
# Allowed values are:
# auth listen for authentication packets
# acct listen for accounting packets
# proxy IP to use for sending proxied packets
# detail Read from the detail file. For examples, see
# raddb/sites-available/copy-acct-to-home-server
# status listen for Status-Server packets. For examples,
# see raddb/sites-available/status
# coa listen for CoA-Request and Disconnect-Request
# packets. For examples, see the file
# raddb/sites-available/coa-server
#
type = auth
# Note: "type = proxy" lets you control the source IP used for
# proxying packets, with some limitations:
#
# * A proxy listener CANNOT be used in a virtual server section.
# * You should probably set "port = 0".
# * Any "clients" configuration will be ignored.
#
# See also proxy.conf, and the "src_ipaddr" configuration entry
# in the sample "home_server" section. When you specify the
# source IP address for packets sent to a home server, the
# proxy listeners are automatically created.
# IP address on which to listen.
# Allowed values are:
# dotted quad (1.2.3.4)
# hostname (radius.example.com)
# wildcard (*)
ipaddr = *
# OR, you can use an IPv6 address, but not both
# at the same time.
# ipv6addr = :: # any. ::1 == localhost
# Port on which to listen.
# Allowed values are:
# integer port number (1812)
# 0 means "use /etc/services for the proper port"
port = 0
# Some systems support binding to an interface, in addition
# to the IP address. This feature isn't strictly necessary,
# but for sites with many IP addresses on one interface,
# it's useful to say "listen on all addresses for eth0".
#
# If your system does not support this feature, you will
# get an error if you try to use it.
#
# interface = eth0
# Per-socket lists of clients. This is a very useful feature.
#
# The name here is a reference to a section elsewhere in
# radiusd.conf, or clients.conf. Having the name as
# a reference allows multiple sockets to use the same
# set of clients.
#
# If this configuration is used, then the global list of clients
# is IGNORED for this "listen" section. Take care configuring
# this feature, to ensure you don't accidentally disable a
# client you need.
#
# See clients.conf for the configuration of "per_socket_clients".
#
# clients = per_socket_clients
}
# This second "listen" section is for listening on the accounting
# port, too.
#
listen {
ipaddr = *
# ipv6addr = ::
port = 0
type = acct
# interface = eth0
# clients = per_socket_clients
}
# hostname_lookups: Log the names of clients or just their IP addresses
# e.g., www.freeradius.org (on) or 206.47.27.232 (off).
#
# The default is 'off' because it would be overall better for the net
# if people had to knowingly turn this feature on, since enabling it
# means that each client request will result in AT LEAST one lookup
# request to the nameserver. Enabling hostname_lookups will also
# mean that your server may stop randomly for 30 seconds from time
# to time, if the DNS requests take too long.
#
# Turning hostname lookups off also means that the server won't block
# for 30 seconds, if it sees an IP address which has no name associated
# with it.
#
# allowed values: {no, yes}
#
hostname_lookups = no
# Core dumps are a bad thing. This should only be set to 'yes'
# if you're debugging a problem with the server.
#
# allowed values: {no, yes}
#
allow_core_dumps = no
# Regular expressions
#
# These items are set at configure time. If they're set to "yes",
# then setting them to "no" turns off regular expression support.
#
# If they're set to "no" at configure time, then setting them to "yes"
# WILL NOT WORK. It will give you an error.
#
regular_expressions = yes
extended_expressions = yes
#
# Logging section. The various "log_*" configuration items
# will eventually be moved here.
#
log {
#
# Destination for log messages. This can be one of:
#
# files - log to "file", as defined below.
# syslog - to syslog (see also the "syslog_facility", below.
# stdout - standard output
# stderr - standard error.
#
# The command-line option "-X" over-rides this option, and forces
# logging to go to stdout.
#
destination = files
#
# The logging messages for the server are appended to the
# tail of this file if destination == "files"
#
# If the server is running in debugging mode, this file is
# NOT used.
#
file = ${logdir}/radius.log
#
# If this configuration parameter is set, then log messages for
# a *request* go to this file, rather than to radius.log.
#
# i.e. This is a log file per request, once the server has accepted
# the request as being from a valid client. Messages that are
# not associated with a request still go to radius.log.
#
# Not all log messages in the server core have been updated to use
# this new internal API. As a result, some messages will still
# go to radius.log. Please submit patches to fix this behavior.
#
# The file name is expanded dynamically. You should ONLY user
# server-side attributes for the filename (e.g. things you control).
# Using this feature MAY also slow down the server substantially,
# especially if you do thinks like SQL calls as part of the
# expansion of the filename.
#
# The name of the log file should use attributes that don't change
# over the lifetime of a request, such as User-Name,
# Virtual-Server or Packet-Src-IP-Address. Otherwise, the log
# messages will be distributed over multiple files.
#
# Logging can be enabled for an individual request by a special
# dynamic expansion macro: %{debug: 1}, where the debug level
# for this request is set to '1' (or 2, 3, etc.). e.g.
#
# ...
# update control {
# Tmp-String-0 = "%{debug:1}"
# }
# ...
#
# The attribute that the value is assigned to is unimportant,
# and should be a "throw-away" attribute with no side effects.
#
requests = ${logdir}/radiusd-%{%{Virtual-Server}:-DEFAULT}-%Y%m%d.log
#
# Which syslog facility to use, if ${destination} == "syslog"
#
# The exact values permitted here are OS-dependent. You probably
# don't want to change this.
#
syslog_facility = daemon
# Log the full User-Name attribute, as it was found in the request.
#
# allowed values: {no, yes}
#
stripped_names = no
# Log authentication requests to the log file.
#
# allowed values: {no, yes}
#
auth = yes
# Log passwords with the authentication requests.
# auth_badpass - logs password if it's rejected
# auth_goodpass - logs password if it's correct
#
# allowed values: {no, yes}
#
auth_badpass = no
auth_goodpass = no
# Log additional text at the end of the "Login OK" messages.
# for these to work, the "auth" and "auth_goopass" or "auth_badpass"
# configurations above have to be set to "yes".
#
# The strings below are dynamically expanded, which means that
# you can put anything you want in them. However, note that
# this expansion can be slow, and can negatively impact server
# performance.
#
# msg_goodpass = ""
# msg_badpass = ""
}
# The program to execute to do concurrency checks.
checkrad = ${sbindir}/checkrad
# SECURITY CONFIGURATION
#
# There may be multiple methods of attacking on the server. This
# section holds the configuration items which minimize the impact
# of those attacks
#
security {
#
# max_attributes: The maximum number of attributes
# permitted in a RADIUS packet. Packets which have MORE
# than this number of attributes in them will be dropped.
#
# If this number is set too low, then no RADIUS packets
# will be accepted.
#
# If this number is set too high, then an attacker may be
# able to send a small number of packets which will cause
# the server to use all available memory on the machine.
#
# Setting this number to 0 means "allow any number of attributes"
max_attributes = 200
#
# reject_delay: When sending an Access-Reject, it can be
# delayed for a few seconds. This may help slow down a DoS
# attack. It also helps to slow down people trying to brute-force
# crack a users password.
#
# Setting this number to 0 means "send rejects immediately"
#
# If this number is set higher than 'cleanup_delay', then the
# rejects will be sent at 'cleanup_delay' time, when the request
# is deleted from the internal cache of requests.
#
# Useful ranges: 1 to 5
reject_delay = 1
#
# status_server: Whether or not the server will respond
# to Status-Server requests.
#
# When sent a Status-Server message, the server responds with
# an Access-Accept or Accounting-Response packet.
#
# This is mainly useful for administrators who want to "ping"
# the server, without adding test users, or creating fake
# accounting packets.
#
# It's also useful when a NAS marks a RADIUS server "dead".
# The NAS can periodically "ping" the server with a Status-Server
# packet. If the server responds, it must be alive, and the
# NAS can start using it for real requests.
#
# See also raddb/sites-available/status
#
status_server = yes
}
# PROXY CONFIGURATION
#
# proxy_requests: Turns proxying of RADIUS requests on or off.
#
# The server has proxying turned on by default. If your system is NOT
# set up to proxy requests to another server, then you can turn proxying
# off here. This will save a small amount of resources on the server.
#
# If you have proxying turned off, and your configuration files say
# to proxy a request, then an error message will be logged.
#
# To disable proxying, change the "yes" to "no", and comment the
# $INCLUDE line.
#
# allowed values: {no, yes}
#
proxy_requests = no
$INCLUDE proxy.conf
# CLIENTS CONFIGURATION
#
# Client configuration is defined in "clients.conf".
#
# The 'clients.conf' file contains all of the information from the old
# 'clients' and 'naslist' configuration files. We recommend that you
# do NOT use 'client's or 'naslist', although they are still
# supported.
#
# Anything listed in 'clients.conf' will take precedence over the
# information from the old-style configuration files.
#
$INCLUDE clients.conf
# THREAD POOL CONFIGURATION
#
# The thread pool is a long-lived group of threads which
# take turns (round-robin) handling any incoming requests.
#
# You probably want to have a few spare threads around,
# so that high-load situations can be handled immediately. If you
# don't have any spare threads, then the request handling will
# be delayed while a new thread is created, and added to the pool.
#
# You probably don't want too many spare threads around,
# otherwise they'll be sitting there taking up resources, and
# not doing anything productive.
#
# The numbers given below should be adequate for most situations.
#
thread pool {
# Number of servers to start initially --- should be a reasonable
# ballpark figure.
start_servers = 5
# Limit on the total number of servers running.
#
# If this limit is ever reached, clients will be LOCKED OUT, so it
# should NOT BE SET TOO LOW. It is intended mainly as a brake to
# keep a runaway server from taking the system with it as it spirals
# down...
#
# You may find that the server is regularly reaching the
# 'max_servers' number of threads, and that increasing
# 'max_servers' doesn't seem to make much difference.
#
# If this is the case, then the problem is MOST LIKELY that
# your back-end databases are taking too long to respond, and
# are preventing the server from responding in a timely manner.
#
# The solution is NOT do keep increasing the 'max_servers'
# value, but instead to fix the underlying cause of the
# problem: slow database, or 'hostname_lookups=yes'.
#
# For more information, see 'max_request_time', above.
#
max_servers = 32
# Server-pool size regulation. Rather than making you guess
# how many servers you need, FreeRADIUS dynamically adapts to
# the load it sees, that is, it tries to maintain enough
# servers to handle the current load, plus a few spare
# servers to handle transient load spikes.
#
# It does this by periodically checking how many servers are
# waiting for a request. If there are fewer than
# min_spare_servers, it creates a new spare. If there are
# more than max_spare_servers, some of the spares die off.
# The default values are probably OK for most sites.
#
min_spare_servers = 3
max_spare_servers = 10
# There may be memory leaks or resource allocation problems with
# the server. If so, set this value to 300 or so, so that the
# resources will be cleaned up periodically.
#
# This should only be necessary if there are serious bugs in the
# server which have not yet been fixed.
#
# '0' is a special value meaning 'infinity', or 'the servers never
# exit'
max_requests_per_server = 0
}
# MODULE CONFIGURATION
#
# The names and configuration of each module is located in this section.
#
# After the modules are defined here, they may be referred to by name,
# in other sections of this configuration file.
#
modules {
#
# Each module has a configuration as follows:
#
# name [ instance ] {
# config_item = value
# ...
# }
#
# The 'name' is used to load the 'rlm_name' library
# which implements the functionality of the module.
#
# The 'instance' is optional. To have two different instances
# of a module, it first must be referred to by 'name'.
# The different copies of the module are then created by
# inventing two 'instance' names, e.g. 'instance1' and 'instance2'
#
# The instance names can then be used in later configuration
# INSTEAD of the original 'name'. See the 'radutmp' configuration
# for an example.
#
#
# As of 2.0.5, most of the module configurations are in a
# sub-directory. Files matching the regex /[a-zA-Z0-9_.]+/
# are loaded. The modules are initialized ONLY if they are
# referenced in a processing section, such as authorize,
# authenticate, accounting, pre/post-proxy, etc.
#
$INCLUDE ${confdir}/modules/
# Extensible Authentication Protocol
#
# For all EAP related authentications.
# Now in another file, because it is very large.
#
$INCLUDE eap.conf
# Include another file that has the SQL-related configuration.
# This is another file only because it tends to be big.
#
# $INCLUDE sql.conf
#
# This module is an SQL enabled version of the counter module.
#
# Rather than maintaining seperate (GDBM) databases of
# accounting info for each counter, this module uses the data
# stored in the raddacct table by the sql modules. This
# module NEVER does any database INSERTs or UPDATEs. It is
# totally dependent on the SQL module to process Accounting
# packets.
#
# $INCLUDE sql/mysql/counter.conf
#
# IP addresses managed in an SQL table.
#
# $INCLUDE sqlippool.conf
}
# Instantiation
#
# This section orders the loading of the modules. Modules
# listed here will get loaded BEFORE the later sections like
# authorize, authenticate, etc. get examined.
#
# This section is not strictly needed. When a section like
# authorize refers to a module, it's automatically loaded and
# initialized. However, some modules may not be listed in any
# of the following sections, so they can be listed here.
#
# Also, listing modules here ensures that you have control over
# the order in which they are initalized. If one module needs
# something defined by another module, you can list them in order
# here, and ensure that the configuration will be OK.
#
instantiate {
#
# Allows the execution of external scripts.
# The entire command line (and output) must fit into 253 bytes.
#
# e.g. Framed-Pool = `%{exec:/bin/echo foo}`
exec
#
# The expression module doesn't do authorization,
# authentication, or accounting. It only does dynamic
# translation, of the form:
#
# Session-Timeout = `%{expr:2 + 3}`
#
# So the module needs to be instantiated, but CANNOT be
# listed in any other section. See 'doc/rlm_expr' for
# more information.
#
expr
#
# We add the counter module here so that it registers
# the check-name attribute before any module which sets
# it
# daily
expiration
logintime
# subsections here can be thought of as "virtual" modules.
#
# e.g. If you have two redundant SQL servers, and you want to
# use them in the authorize and accounting sections, you could
# place a "redundant" block in each section, containing the
# exact same text. Or, you could uncomment the following
# lines, and list "redundant_sql" in the authorize and
# accounting sections.
#
#redundant redundant_sql {
# sql1
# sql2
#}
}
######################################################################
#
# Policies that can be applied in multiple places are listed
# globally. That way, they can be defined once, and referred
# to multiple times.
#
######################################################################
$INCLUDE policy.conf
######################################################################
#
# Load virtual servers.
#
# This next $INCLUDE line loads files in the directory that
# match the regular expression: /[a-zA-Z0-9_.]+/
#
# It allows you to define new virtual servers simply by placing
# a file into the raddb/sites-enabled/ directory.
#
$INCLUDE sites-enabled/
######################################################################
#
# All of the other configuration sections like "authorize {}",
# "authenticate {}", "accounting {}", have been moved to the
# the file:
#
# raddb/sites-available/default
#
# This is the "default" virtual server that has the same
# configuration as in version 1.0.x and 1.1.x. The default
# installation enables this virtual server. You should
# edit it to create policies for your local site.
#
# For more documentation on virtual servers, see:
#
# raddb/sites-available/README
#
######################################################################Im Bereich "MODULE CONFIGURATION" steht, dass viele Modul configs nach /etc/freeradius/modules/ ausgelagert wurden.
Da ich einen Ldap-Server eintragen möchte schaue ich mir die /etc/freeradius/modules/ldap an.
-- Hier meine /etc/freeradius/modules/ldap vom Radius-Server.
ldap {
server = 172.26.100.1
basedn = "dc=tarent,dc=de"
filter = "(uid=%{%{Stripped-User-Name}:-%{User-Name}})"
base_filter = "(objectclass=posixAccount)"
groupname_attribute = cn
dictionary_mapping = /etc/freeradius/ldap.attrmap
password_attribute = userPassword
set_auth_type = yes
}Die /etc/freeradius/modules/ldap war vorher leer, es stand nur "ldap{}" drin.
Dann habe ich meinen Ldap Server dort eingetragen und jetzt sieht die /etc/freeradius/modules/ldap so aus wie oben zu sehen.
Weil ich dann mal testen wollte ob der Radius-Server auch mit dem Ldap Server spricht habe ich den Befehl "radtest" rausgekramt.
-- Der Befehl radtest
[root@radius-bn-01 ~]# radtest ?
Usage: radtest [OPTIONS] user passwd radius-server[:port] nas-port-number secret [ppphint] [nasname]
-d RADIUS_DIR Set radius directory
-t <type> Set authentication method
type can be pap, chap, mschap, or eap-md5
-x Enable debug output-- Erster Versuch mit radtest
[root@radius-bn-01 ~]# radtest testuser passwort123 172.26.100.1:389 10 testing123
Sending Access-Request of id 146 to 172.26.100.1 port 389
User-Name = "testuser"
User-Password = "passwort123"
NAS-IP-Address = 10.10.20.36
NAS-Port = 10
radclient: no response from server for ID 146 socket 3testuser und passwort123 sind verfremdet, aber garantiert im Ldap vorhanden. Richtig sind die Zugangsdaten auch.
172.26.100.1 ist die IP-Adresse vom Radius-Server.
Die NAS-Port-Number kann man sich laut http://linux.die.net/man/1/radtest aussuchen.
Das Secret ist das was ich vorher in der /etc/freeradius/clients.conf festgelegt habe.
-- Zweiter Versuch mit radtest
[root@radius-bn-01 ~]# radtest testuser passwort123 127.0.0.1 0 testing123
Sending Access-Request of id 242 to 127.0.0.1 port 1812
User-Name = "testuser"
User-Password = "passwort123"
NAS-IP-Address = 10.10.20.36
NAS-Port = 0
rad_recv: Access-Reject packet from host 127.0.0.1 port 1812, id=242, length=20Ähnlich wie der erste Versuch, diesmal allerdings mit der localhost Adresse.
Beim Radius-Server bekomme ich dann folgende Reaktion raus.
-- Radius-Server Reaktion auf meinen zweiten Login Versuch
rad_recv: Access-Request packet from host 127.0.0.1 port 36972, id=242, length=58
User-Name = "testuser"
User-Password = "passwort123"
NAS-IP-Address = 10.10.20.36
NAS-Port = 0
# Executing section authorize from file /etc/freeradius/sites-enabled/inner-tunnel
+- entering group authorize {...}
++[chap] returns noop
++[mschap] returns noop
[eap] No EAP-Message, not doing EAP
++[eap] returns noop
[ldap] performing user authorization for testuser
[ldap] expand: %{Stripped-User-Name} ->
[ldap] ... expanding second conditional
[ldap] expand: %{User-Name} -> testuser
[ldap] expand: (uid=%{%{Stripped-User-Name}:-%{User-Name}}) -> (uid=testuser)
[ldap] expand: dc=tarent,dc=de -> dc=tarent,dc=de
[ldap] ldap_get_conn: Checking Id: 0
[ldap] ldap_get_conn: Got Id: 0
[ldap] attempting LDAP reconnection
[ldap] (re)connect to 172.26.100.1:389, authentication 0
[ldap] bind as / to 172.26.100.1:389
[ldap] waiting for bind result ...
[ldap] Bind was successful
[ldap] performing search in dc=tarent,dc=de, with filter (uid=testuser)
[ldap] No default NMAS login sequence
[ldap] looking for check items in directory...
[ldap] looking for reply items in directory...
WARNING: No "known good" password was found in LDAP. Are you sure that the user is configured correctly?
[ldap] Setting Auth-Type = LDAP
[ldap] user farenz authorized to use remote access
[ldap] ldap_release_conn: Release Id: 0
++[ldap] returns ok
Found Auth-Type = LDAP
# Executing group from file /etc/freeradius/sites-enabled/inner-tunnel
+- entering group LDAP {...}
[ldap] login attempt by "testuser" with password "passwort123"
[ldap] user DN: uid=testuser,cn=users,dc=tarent,dc=de
[ldap] (re)connect to 172.26.100.1:389, authentication 1
[ldap] bind as uid=testuser,cn=users,dc=tarent,dc=de/passwort123 to 172.26.100.1:389
[ldap] waiting for bind result ...
[ldap] Bind was successful
[ldap] user testuser authenticated succesfully
++[ldap] returns ok
Login OK: [testuser] (from client localhost port 0)
# Executing section post-auth from file /etc/freeradius/sites-enabled/inner-tunnel
+- entering group post-auth {...}
++? if (!(Ldap-Group == "WLAN" ))
[ldap] Entering ldap_groupcmp()
expand: dc=tarent,dc=de -> dc=tarent,dc=de
expand: (|(&(objectClass=GroupOfNames)(member=%{Ldap-UserDn}))(&(objectClass=GroupOfUniqueNames)(uniquemember=%{Ldap-UserDn}))) -> (|(&(objectClass=GroupOfNames)(member=))(&(objectClass=GroupOfUniqueNames)(uniquemember=)))
[ldap] ldap_get_conn: Checking Id: 0
[ldap] ldap_get_conn: Got Id: 0
[ldap] performing search in dc=tarent,dc=de, with filter (&(cn=WLAN)(|(&(objectClass=GroupOfNames)(member=))(&(objectClass=GroupOfUniqueNames)(uniquemember=))))
[ldap] object not found
[ldap] ldap_release_conn: Release Id: 0
rlm_ldap::ldap_groupcmp: Group WLAN not found or user is not a member.
?? Evaluating (Ldap-Group == "WLAN" ) -> FALSE
? Converting !FALSE -> TRUE
++? if (!(Ldap-Group == "WLAN" )) -> TRUE
++- entering if (!(Ldap-Group == "WLAN" )) {...}
+++[fail] returns fail
++- if (!(Ldap-Group == "WLAN" )) returns fail
Delaying reject of request 0 for 1 seconds
Going to the next request
Waking up in 0.9 seconds.
Sending delayed reject for request 0
Sending Access-Reject of id 242 to 127.0.0.1 port 36972
Waking up in 4.9 seconds.
Cleaning up request 0 ID 242 with timestamp +5825
Ready to process requests.Daraus habe ich entnommen, dass der testuser nicht in der LDAP-Gruppe WLAN ist. Als ich den testuser aber hinzugefügt habe und die Anfrage immer noch nicht geklappt hat, habe ich mir die Debug-Ausgabe gründlicher durchgelesen und festgestellt, dass der Standard "groupmembership-filter" verwendet wird, welcher in der /etc/freeradius/sites-enabled/inner-tunnel definiert ist.
Also habe ich mir einen neuen "groupmembership-filter" gebastelt.
ldap {
server = 172.26.100.1
basedn = "dc=tarent,dc=de"
filter = "(uid=%{%{Stripped-User-Name}:-%{User-Name}})"
base_filter = "(objectclass=posixAccount)"
groupname_attribute = cn
# groupmembership_filter = "(|(&(objectClass=GroupOfNames)(member=%{control:Ldap-UserDn}))(&(objectClass=GroupOfUniqueNames)(uniquemember=%{control:Ldap-UserDn})))"
groupmembership_filter = "(&(objectClass=posixGroup)(memberUid=%{%{Stripped-User-Name}:-%{User-Name}}))"
# groupmembership_attribute = radiusGroupName
groupmembership_attribute = WLAN
# compare_check_items = yes
# do_xlat = yes
# access_attr_used_for_allow = yes
dictionary_mapping = /etc/freeradius/ldap.attrmap
password_attribute = userPassword
set_auth_type = yes
}Welcher überraschenderweise funktioniert.
-- Nächster Versuch mit radtest
radtest -x testuser passwort123 127.0.0.1 10 testing123
Sending Access-Request of id 197 to 127.0.0.1 port 1812
User-Name = "testuser"
User-Password = "passwort123"
NAS-IP-Address = 10.10.20.36
NAS-Port = 10
rad_recv: Access-Accept packet from host 127.0.0.1 port 1812, id=197, length=20Nun stehe ich vor der Herausforderung meinen Cisco Access Point dazu zu bringen mit meinem Radius-Server zu sprechen.
Bitten und betteln sowie dem AP gut zureden hat bis jetzt nicht funktioniert. Genau so wenig wie einige der vielen Tutorials welche ich in den untiefen des Internets (unter anderem auch hier auf administrator.de) gefunden habe.
Hat jemand einen Tipp für mich oder vielleicht auch eine Anleitung wie ich meinen Cisco Aironet 1130ag konfigurieren muss damit er mit meinem Radius spricht?
Auf der Weboberfläche des AP habe ich den Radius-Server eingetragen, allerdings sieht es so aus, dass die Anfrage nie beim Radius ankommt. Kann ich dem AP irgendwie die Logfiles entlocken? Vielleicht über das Terminal per ssh Verbindung?
-- Ein telnet von meinem AP auf den Radius-Server funktioniert nicht.
telnet 10.10.20.36 1812
Trying 10.10.20.36, 1812 ...
% Connection refused by remote host-- netstat -tulpen sagt mir, dass der Radius-Server aber eigentlich zuhören sollte.
netstat -tulpen
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State User Inode PID/Program name
...
udp 0 0 0.0.0.0:1812 0.0.0.0:* 104 156230 1935/freeradius
udp 0 0 0.0.0.0:1813 0.0.0.0:* 104 156233 1935/freeradius
... Bin mittlerweile zu dem Schluss gekommen, dass telnet kein udp kann.
Bei einem telnet auf einen port der tcp kann kam der Kommentar "Open" zurück.
Vielen Dank und viele Grüße
farenz
Please also mark the comments that contributed to the solution of the article
Content-Key: 191133
Url: https://administrator.de/contentid/191133
Printed on: April 25, 2024 at 01:04 o'clock
8 Comments
Latest comment
Hi
Ist schon sehr lange her wo ich das mal ausprobiert habe ...
Aber evtl. hilft's ja
Meine Konfig sah damals so aus:
version 12.4
no service pad
service timestamps debug datetime msec
service timestamps log datetime msec
service password-encryption
!
hostname TESTWLAN
!
enable secret 5
!
aaa new-model
!
!
aaa group server radius rad_eap
server 10.10.10.100 auth-port 1645 acct-port 1646
server 10.11.10.101 auth-port 1645 acct-port 1646
!
aaa group server radius rad_mac
!
aaa group server radius rad_acct
!
aaa group server radius rad_admin
!
aaa group server tacacs+ tac_admin
!
aaa group server radius rad_pmip
!
aaa group server radius dummy
!
aaa authentication login eap_methods group rad_eap
aaa authentication login mac_methods local
aaa authorization exec default local
aaa accounting network acct_methods start-stop group rad_acct
!
aaa session-id common
ip domain name mydomain.com
ip name-server 10.10.9.100
!
!
!
dot11 ssid USERWLAN
vlan 56
authentication open eap eap_methods
authentication key-management wpa
!
dot11 ssid PDAWLAN
vlan 55
authentication open eap eap_methods
authentication key-management wpa
!
dot11 network-map
power inline negotiation prestandard source
!
!
username * password
!
bridge irb
!
!
interface Dot11Radio0
no ip address
no ip route-cache
!
encryption vlan 56 mode ciphers tkip
!
encryption vlan 1 mode ciphers tkip
!
encryption vlan 55 mode ciphers tkip
!
broadcast-key vlan 56 change 600
!
broadcast-key vlan 55 change 600
!
!
ssid USERWLAN
!
ssid PDAWLAN
!
station-role root
!
interface Dot11Radio0.1
encapsulation dot1Q 1 native
no ip route-cache
bridge-group 1
bridge-group 1 subscriber-loop-control
bridge-group 1 block-unknown-source
no bridge-group 1 source-learning
no bridge-group 1 unicast-flooding
bridge-group 1 spanning-disabled
!
interface Dot11Radio0.55
encapsulation dot1Q 55
no ip route-cache
bridge-group 55
bridge-group 55 subscriber-loop-control
bridge-group 55 block-unknown-source
no bridge-group 55 source-learning
no bridge-group 55 unicast-flooding
bridge-group 55 spanning-disabled
!
interface Dot11Radio0.56
encapsulation dot1Q 56
no ip route-cache
bridge-group 56
bridge-group 56 subscriber-loop-control
bridge-group 56 block-unknown-source
no bridge-group 56 source-learning
no bridge-group 56 unicast-flooding
bridge-group 56 spanning-disabled
!
interface Dot11Radio1
no ip address
no ip route-cache
shutdown
no dfs band block
channel dfs
station-role root
bridge-group 1
bridge-group 1 subscriber-loop-control
bridge-group 1 block-unknown-source
no bridge-group 1 source-learning
no bridge-group 1 unicast-flooding
bridge-group 1 spanning-disabled
!
interface FastEthernet0
no ip address
no ip route-cache
speed 100
full-duplex
bridge-group 1
no bridge-group 1 source-learning
bridge-group 1 spanning-disabled
!
interface FastEthernet0.55
encapsulation dot1Q 55
no ip route-cache
bridge-group 55
no bridge-group 55 source-learning
bridge-group 55 spanning-disabled
!
interface FastEthernet0.56
encapsulation dot1Q 56
no ip route-cache
bridge-group 56
no bridge-group 56 source-learning
bridge-group 56 spanning-disabled
!
interface BVI1
ip address 10.10.200.100 255.255.254.0
no ip route-cache
!
ip default-gateway 10.10.200.1
no ip http server
no ip http secure-server
ip http help-path http://www.cisco.com/warp/public/779/smbiz/prodconfig/help/eag
ip radius source-interface BVI1
logging trap notifications
logging source-interface BVI1
logging 10.10.200.200
access-list 13 permit 10.10.10.0 0.0.0.255
access-list 13 deny any log
access-list 19 deny any log
access-list 20 permit 20.130.15.41
access-list 20 deny any log
access-list 99 permit 10.10.200.200
access-list 99 permit 10.10.10.9
access-list 99 permit 10.10.10.100
access-list 99 permit 10.10.10.200
access-list 99 permit 10.10.11.200
access-list 199 permit ip any any log
snmp-server community * RO 13
snmp-server community * RW 20
snmp-server community * RO 19
snmp-server location Test
snmp-server contact Test
snmp-server system-shutdown
snmp-server enable traps tty
snmp-server host 10.10.200.200
snmp-server host 10.10.200.200
radius-server attribute 32 include-in-access-req format %h
radius-server host 10.10.10.100 auth-port 1645 acct-port 1646 key
radius-server host 10.10.10.101 auth-port 1645 acct-port 1646 key
radius-server vsa send accounting
bridge 1 route ip
!
!
banner login ^CCC SECURITY NOTICE
If you are not an authorised user please disconnect immediately. ^C
!
line con 0
exec-timeout 5 0
password
logging synchronous
transport output all
line vty 0 4
session-timeout 60
access-class 199 in
exec-timeout 15 0
password 7
logging synchronous
transport input telnet
transport output all
line vty 5 15
session-timeout 60
access-class 199 in
exec-timeout 15 0
password 7
logging synchronous
transport input telnet
!
sntp server 10.10.10.222
end
Ist schon sehr lange her wo ich das mal ausprobiert habe ...
Aber evtl. hilft's ja
Meine Konfig sah damals so aus:
version 12.4
no service pad
service timestamps debug datetime msec
service timestamps log datetime msec
service password-encryption
!
hostname TESTWLAN
!
enable secret 5
!
aaa new-model
!
!
aaa group server radius rad_eap
server 10.10.10.100 auth-port 1645 acct-port 1646
server 10.11.10.101 auth-port 1645 acct-port 1646
!
aaa group server radius rad_mac
!
aaa group server radius rad_acct
!
aaa group server radius rad_admin
!
aaa group server tacacs+ tac_admin
!
aaa group server radius rad_pmip
!
aaa group server radius dummy
!
aaa authentication login eap_methods group rad_eap
aaa authentication login mac_methods local
aaa authorization exec default local
aaa accounting network acct_methods start-stop group rad_acct
!
aaa session-id common
ip domain name mydomain.com
ip name-server 10.10.9.100
!
!
!
dot11 ssid USERWLAN
vlan 56
authentication open eap eap_methods
authentication key-management wpa
!
dot11 ssid PDAWLAN
vlan 55
authentication open eap eap_methods
authentication key-management wpa
!
dot11 network-map
power inline negotiation prestandard source
!
!
username * password
!
bridge irb
!
!
interface Dot11Radio0
no ip address
no ip route-cache
!
encryption vlan 56 mode ciphers tkip
!
encryption vlan 1 mode ciphers tkip
!
encryption vlan 55 mode ciphers tkip
!
broadcast-key vlan 56 change 600
!
broadcast-key vlan 55 change 600
!
!
ssid USERWLAN
!
ssid PDAWLAN
!
station-role root
!
interface Dot11Radio0.1
encapsulation dot1Q 1 native
no ip route-cache
bridge-group 1
bridge-group 1 subscriber-loop-control
bridge-group 1 block-unknown-source
no bridge-group 1 source-learning
no bridge-group 1 unicast-flooding
bridge-group 1 spanning-disabled
!
interface Dot11Radio0.55
encapsulation dot1Q 55
no ip route-cache
bridge-group 55
bridge-group 55 subscriber-loop-control
bridge-group 55 block-unknown-source
no bridge-group 55 source-learning
no bridge-group 55 unicast-flooding
bridge-group 55 spanning-disabled
!
interface Dot11Radio0.56
encapsulation dot1Q 56
no ip route-cache
bridge-group 56
bridge-group 56 subscriber-loop-control
bridge-group 56 block-unknown-source
no bridge-group 56 source-learning
no bridge-group 56 unicast-flooding
bridge-group 56 spanning-disabled
!
interface Dot11Radio1
no ip address
no ip route-cache
shutdown
no dfs band block
channel dfs
station-role root
bridge-group 1
bridge-group 1 subscriber-loop-control
bridge-group 1 block-unknown-source
no bridge-group 1 source-learning
no bridge-group 1 unicast-flooding
bridge-group 1 spanning-disabled
!
interface FastEthernet0
no ip address
no ip route-cache
speed 100
full-duplex
bridge-group 1
no bridge-group 1 source-learning
bridge-group 1 spanning-disabled
!
interface FastEthernet0.55
encapsulation dot1Q 55
no ip route-cache
bridge-group 55
no bridge-group 55 source-learning
bridge-group 55 spanning-disabled
!
interface FastEthernet0.56
encapsulation dot1Q 56
no ip route-cache
bridge-group 56
no bridge-group 56 source-learning
bridge-group 56 spanning-disabled
!
interface BVI1
ip address 10.10.200.100 255.255.254.0
no ip route-cache
!
ip default-gateway 10.10.200.1
no ip http server
no ip http secure-server
ip http help-path http://www.cisco.com/warp/public/779/smbiz/prodconfig/help/eag
ip radius source-interface BVI1
logging trap notifications
logging source-interface BVI1
logging 10.10.200.200
access-list 13 permit 10.10.10.0 0.0.0.255
access-list 13 deny any log
access-list 19 deny any log
access-list 20 permit 20.130.15.41
access-list 20 deny any log
access-list 99 permit 10.10.200.200
access-list 99 permit 10.10.10.9
access-list 99 permit 10.10.10.100
access-list 99 permit 10.10.10.200
access-list 99 permit 10.10.11.200
access-list 199 permit ip any any log
snmp-server community * RO 13
snmp-server community * RW 20
snmp-server community * RO 19
snmp-server location Test
snmp-server contact Test
snmp-server system-shutdown
snmp-server enable traps tty
snmp-server host 10.10.200.200
snmp-server host 10.10.200.200
radius-server attribute 32 include-in-access-req format %h
radius-server host 10.10.10.100 auth-port 1645 acct-port 1646 key
radius-server host 10.10.10.101 auth-port 1645 acct-port 1646 key
radius-server vsa send accounting
bridge 1 route ip
!
!
banner login ^CCC SECURITY NOTICE
If you are not an authorised user please disconnect immediately. ^C
!
line con 0
exec-timeout 5 0
password
logging synchronous
transport output all
line vty 0 4
session-timeout 60
access-class 199 in
exec-timeout 15 0
password 7
logging synchronous
transport input telnet
transport output all
line vty 5 15
session-timeout 60
access-class 199 in
exec-timeout 15 0
password 7
logging synchronous
transport input telnet
!
sntp server 10.10.10.222
end
Ansonsten findest du auch hier weitere Infos:
Sichere 802.1x WLAN-Benutzer Authentisierung über Radius
Sichere 802.1x WLAN-Benutzer Authentisierung über Radius